EternalBlue (MS17-010): The Exploit That Powered WannaCry
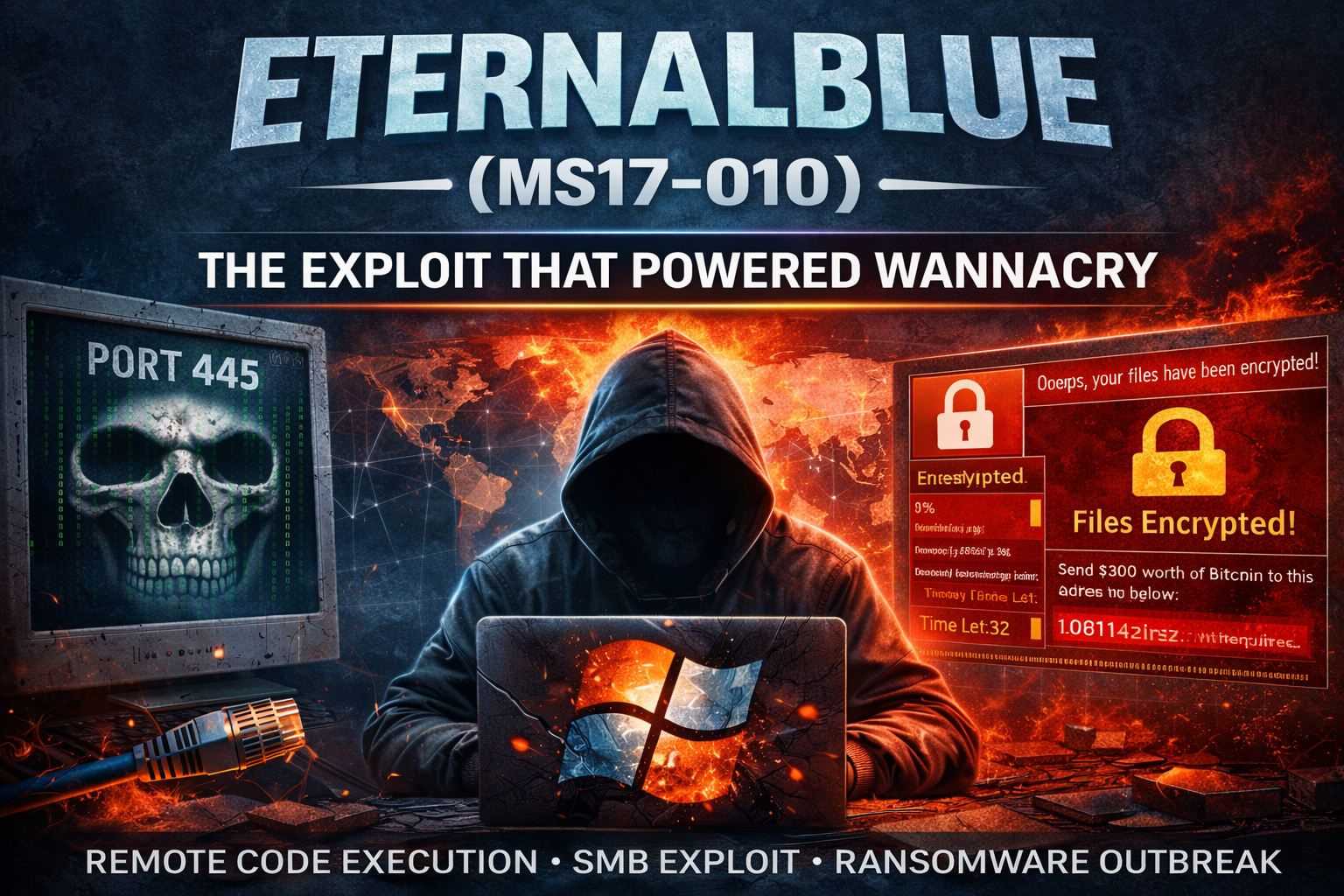
In 2017, a leaked NSA exploit known as EternalBlue changed cybersecurity forever.
Targeting a flaw in Microsoft’s SMBv1 protocol (MS17-010), EternalBlue allowed unauthenticated remote code execution over TCP port 445. An attacker could send a specially crafted SMB packet and gain SYSTEM-level access to a vulnerable Windows machine — no credentials required.
The exploit abused improper memory handling in SMB transaction requests, leading to kernel-level code execution.
It became globally infamous when it was weaponized by WannaCry, which spread automatically across networks, infecting over 200,000 systems in more than 150 countries within days.
Why it was so dangerous:
- No user interaction needed
- Wormable across internal networks
- Full system compromise
- Massive real-world impact
Microsoft patched the issue under MS17-010, and SMBv1 has since been deprecated — yet vulnerable systems still appear during internal security assessments.
EternalBlue remains a textbook example of how a single unpatched service can escalate into a global cyber crisis.
Proof of Concept
Read the full article: https://luckyy.uk/eternalblue-ms17-010-the-exploit-that-powered-wannacry/
- Tech
- Art
- Causes
- Crafts
- Dance
- Drinks
- Film
- Fitness
- Food
- Oyunlar
- Gardening
- Health
- Home
- Literature
- Music
- Networking
- Other
- Party
- Religion
- Shopping
- Sports
- Theater
- Wellness
